An extraction has two types of settings:
- Extraction Settings include settings that affect only the respective extraction type.
- General Settings are the same for all extraction types.
General Settings are independent of the extraction type.
To Open General Settings #
- In the main window of the Designer, double-click an extraction.
The main window of the component opens.
Example: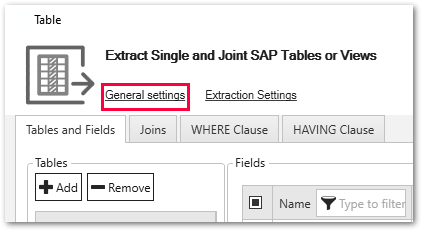
- Within the opened window, click [General Settings].
The window “General Settings” opens.
Misc. Tab #
The miscellaneous tab consists of two subsections:
- Options
- Keywords
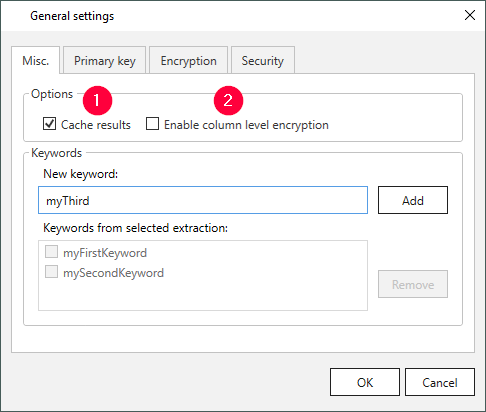
Options
Cache results (1)
Note: The Cache results option is only available in pull destinations (e.g., PBI, Qlik etc.).
Pull destinations often pull the data from SAP for several times. To decrease the SAP server load, you can select the Cache results option, this way the pull destination pulls the data from cache and not from the SAP.
This increases the performance and limits the impact on the SAP system. If this behavior is not desired (for example, because the data must be always 100% up to date), the cache option must be explicitly turned off.
Enable column level encryption (2)
This option needs to be active when using “Column Encryption”, see Encryption.
Keywords
One or more keywords (Tags) can be set to an extraction. Keywords can be entered directly in the keyword field. Within the Designer you can use these keywords to filter extractions.
Tip: To add keywords to multiple extractions at once, select the extractions in the main window of the Designer. Via right-click + Add/Remove keywords the window “Add/Remove Keywords To/From Multiple Extractions” opens.
Primary Key Tab #
Table extractions inherit the primary keys from SAP. Other objects such as SAP Query, BW Cube etc. require manual setting of the primary keys.
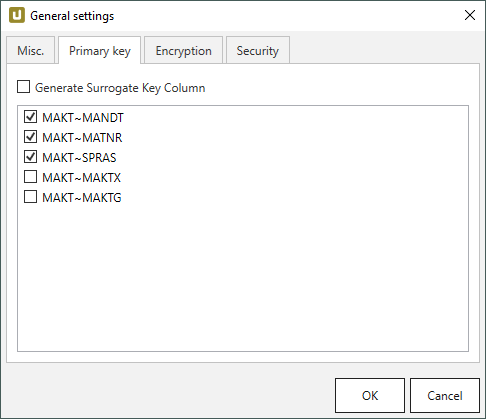
The example above shows the SAP object MAKT with its primary key inherited from SAP in the general settings of the Designer. In this example the primary key consists of MANDT, MATNR and SPRAS. The primary key is also taken over in the destination.
Note: A defined primary key field in a table is a prerequisite for merging data.
Generate Surrogate Key Column:
If this option is active, an additional column THEO_SURR_KEY is added to the extracted data.
The THEO_SURR_KEY column contains surrogate keys that can be used as row IDs.
The surrogate keys are hash values of type signed 8 byte integer, e.g., #-3008591679982390000.
They are generated from the selected primary key columns and the name of the SAP source that is assigned to the extraction.
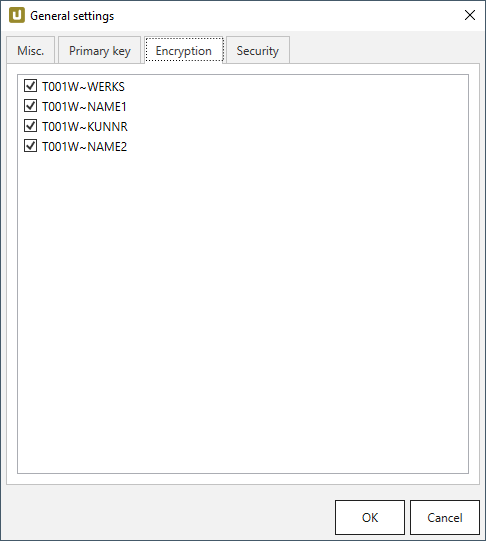
Encryption Tab #
The “Column Encryption” feature enables users to encrypt columns in the extracted data set, before uploading them to the destination.
By encrypting the columns you can ensure the safety of sensitive information. You can store data in its encrypted form or decrypt it immediately.
The feature also supports random access, meaning that the data is decryptable at any starting point. Because random access has a significant overhead, it is not recommended to use column encryption for encrypting the whole data set.
Not all destinations support column encryption.
If the column encryption feature is available, you can select the columns to encrypt from a list of available columns.
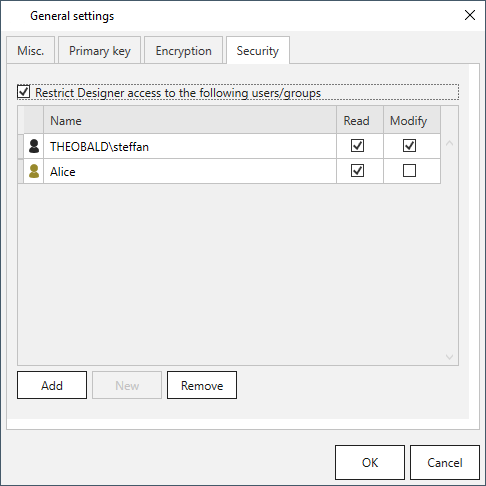
Security Tab #
The security tab is described in the section access management.
Columns Order Tab #
The “Columns Order” feature enables users to rearrange the order of result columns when running an extraction.
To rearrange the result order, assign indexes to the available result columns.
Index 0 defines the first column in the result set, index 1 the second columns, etc.
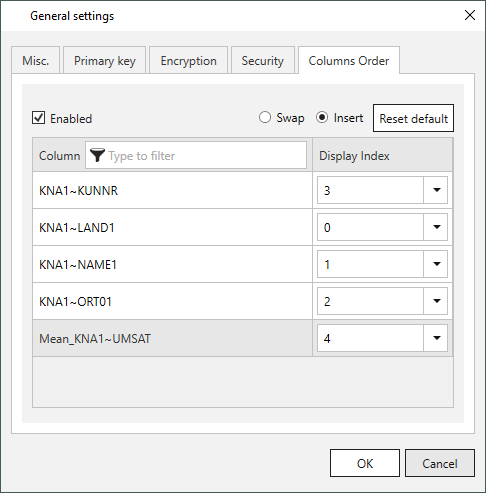
Enabled:
If this option is active, a new column order is applied when running the extraction.
Swap:
Swaps the index of 2 columns. All other columns keep their indexes.
Insert:
Inserts the selected column into the selected index. All other indexes are recalculated.
[Reset default]:
Restores the original column order.