About #
This section is about restricting access to Xtract Universal/Board Connector’s built in web server to predefined users or user groups.
By setting access restrictions on the web server you ensure that only dedicated users can execute extractions.
There are two types of users and user groups, access can be restricted to.
- Windows AD users (Kerberos authentication)
- custom users (Basic authentication)
When access to the web server is restricted, Windows AD credentials or credentials of a custom user must be submitted when running an extraction.
Prerequisite: Activating TLS encryption #
Both types of access restrictions require accessing the web server through an https connection. This requires installation of an X.509 certificate. If the certificate is not listed in the Windows certificate store, install the X.509 certificate.
- Navigate to the menu bar and select Server > Settings. Switch to the Web Server tab.
- Depending on what type of user you want to restrict access to, select HTTPS - Restricted to AD users with Designer read access or HTTPS - Restricted to custom users with Designer read access.
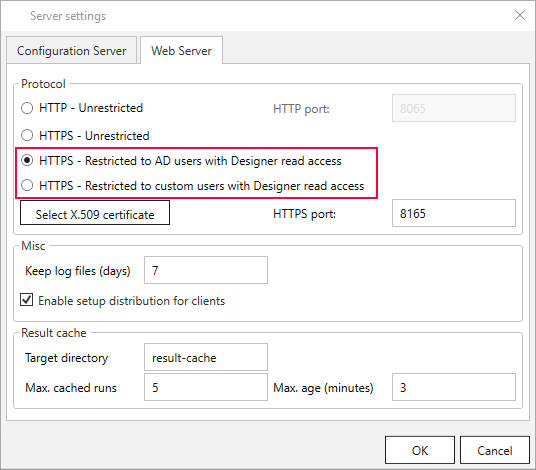
- Click the [Select X.509 certificate] button. The “Edit certificate location” window opens.
- Select the X.509 certificate created for your machine under Local Machine > Personal.
- Confirm with [OK]. The window closes.
- Optional: Change the port number of the HTTPS port.
Restrict access to Windows AD users (Kerberos authentication) #
- Assign a Windows service account under which the Xtract Universal/Board Connector service runs. See Running a service under a Windows service account.
- Activate TLS encryption as outlined in Prerequisite: Activating TLS encryption.
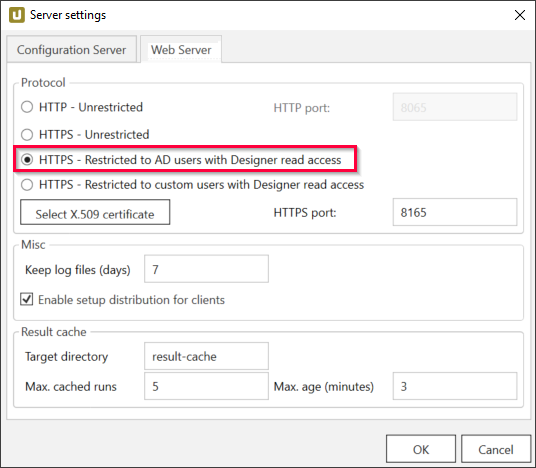
- Navigate to the menu bar and select Server > Settings. In the Web Server tab select HTTPS - Restricted to AD users with Designer read access.
- Switch to the Configuration Server tab.
- Add the custom users or groups that are allowed to execute an extraction to Access Management.
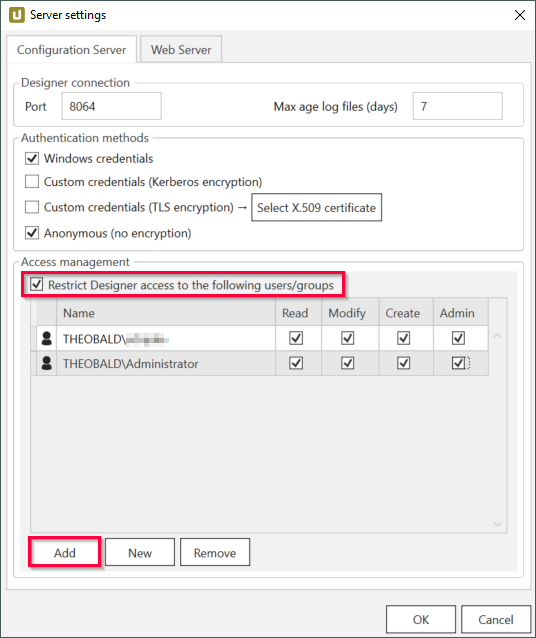
- Assign at least Read permission to the Windows AD users.
- Close all windows with [OK]
- Restart the server when prompted.
Result: An extraction can only be executed, if the Windows AD credentials of the caller are passed on to the web server and the caller has at least Read access to the Designer.
Note: This type of authentication uses Kerberos authentication via SPNEGO. NTLM is not supported.
Restrict access to custom users (Basic authentication) #
- Activate TLS encryption as outlined in the section Prerequisite: Activating TLS encryption.
- Navigate to the menu bar and select Server > Settings. In the Web Server tab select HTTPS - Restricted to custom users with Designer read access
- Switch to the Configuration Server tab.
- Add the Windows AD users or groups that are allowed to execute an extraction to Access Management.
- Assign at least Read permission to the custom users.
- Close all Windows with [OK]
- Restart the server when prompted.
Result: An extraction can only be executed, if the custom credentials of the caller are passed on to the web server and the caller has at least Read access to the Designer.
Note: For information on how to call an extraction with Basic Authentication through xu.exe, see Basic Authentication via Commandline.
Running a service under a Windows service account #
When restricting access to Windows AD users, the Xtract Universal service must run under a dedicated service account. To do that, follow the steps in Running the Xtract Universal Service under a Windows Service Account.